Beware of Holiday Cyber Scams in 2024

As the 2024 holiday season approaches, the excitement of shopping and gift-giving is in the air. However, it’s also a prime time for cybercriminals who are eager to exploit the festive rush. Understanding the top holiday cyber scams can help protect yourself and your loved ones during this joyous yet vulnerable time. The Rise of […]
Rethinking Cyber Resilience: Safeguarding Against Threats in the Generative AI Era

In today’s rapidly evolving digital landscape, cybersecurity is no longer just about defense; it’s about resilience. As generative AI (Gen AI) becomes more widespread, the threats accompanying it also increase. Cybercriminals are adopting Gen AI-powered attacks like sophisticated phishing schemes and ransomware, targeting industries with advanced technology infrastructures. This new era of cyber threats requires […]
Cybersecurity Horror Stories: Real-Life Attacks That Could Have Been Prevented

Tales of Cyber Disasters In the digital age, cyberattacks are becoming more frequent, sophisticated, and devastating. These horror stories often stem from simple mistakes or overlooked vulnerabilities, leading to severe financial and reputational damage. Whether it’s ransomware paralyzing an organization or phishing scams duping employees, these attacks highlight the importance of proactive cybersecurity measures. Fortunately, […]
Trick or Treat: How Hackers Use Social Engineering to Gain Access

The Deceptive World of Social Engineering Social engineering attacks are some of the most effective tricks used by cybercriminals. By manipulating human emotions like trust, urgency, or fear, hackers deceive individuals into giving up confidential information or access to secure systems. From phishing emails to impersonating employees, these tactics allow criminals to bypass even the […]
Maximize Your IT Budget: Start Planning Now

As we move deeper into 2024, now is the ideal time to review and optimize your IT budget. A well-planned budget not only ensures your IT infrastructure operates smoothly but also positions your business to adapt to emerging technologies and stay competitive. By carefully assessing your current needs and anticipating future demands, you can create […]
Ready for Anything: Strengthening Your IT Infrastructure for Year-End Demands

As we approach the final quarter of the year, businesses across all industries often face a surge in activity. Whether it’s closing deals, processing data, or ramping up production, the demands on your IT infrastructure can escalate quickly. Ensuring that your systems are robust enough to handle these pressures is crucial to maintaining smooth operations […]
Preparing for a Cyber-Safe School Year: Essential IT and Cybersecurity Tips for Students and Parents

As the new school year approaches, students and parents are gearing up for a fresh start. Technology plays a crucial role in education, making it imperative to prioritize IT and cybersecurity. Ensuring that devices and online activities are secure can safeguard sensitive information and create a safe learning environment. Here are essential IT and cybersecurity […]
Lessons to Learn from the CrowdStrike Outage
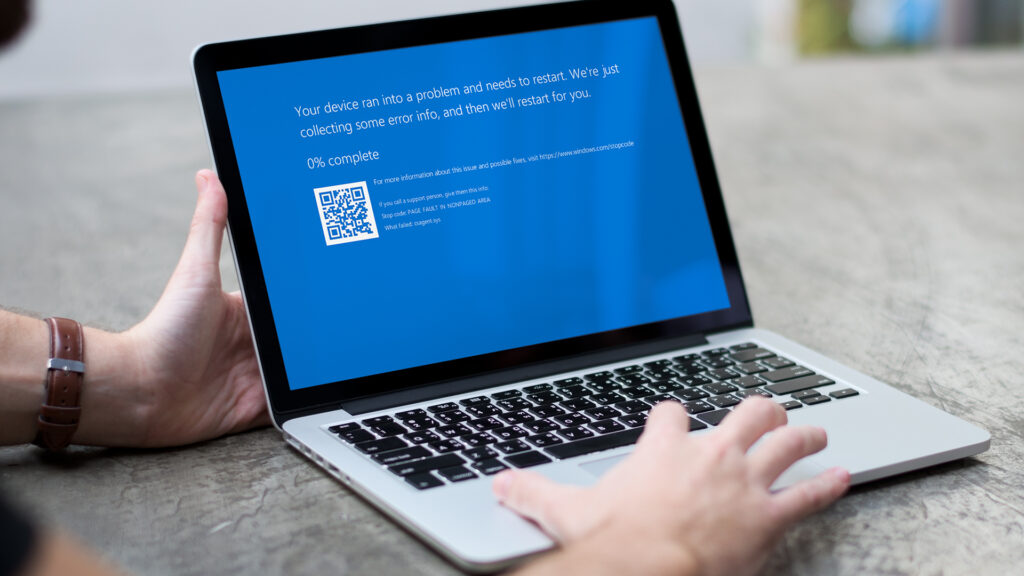
The recent CrowdStrike outage serves as a significant wake-up call for businesses relying on cybersecurity solutions. CrowdStrike’s temporary service disruption, as one of the leading providers of endpoint security, underscores the importance of preparedness and resilience in the face of unexpected technological failures. This incident provides valuable insights into how businesses can strengthen their own […]
Don’t Copy & Paste This Dangerous Text

A new warning for Google Chrome users has emerged, carrying a critical yet straightforward piece of advice: avoid copying and pasting unfamiliar text into your terminal or run dialog box. This advice comes from cybersecurity firm Proofpoint, which has identified a new technique cybercriminals are using to spread malware. The Nature of the Threat Proofpoint […]
Boost Your Smartphone Security: Why the FBI Advises Regular Reboots Matter

Have you ever considered why your smartphone might benefit from a regular reboot? The Federal Bureau of Investigation (FBI) advises a simple yet effective practice: regularly rebooting your phone. This recommendation, backed by cybersecurity experts, plays a crucial role in maintaining your device’s security and integrity. The Importance of Regular Reboots Our smartphones contain a […]
